
Burp-Suite is a IT security tool usefull for testing web applications. Its feature is capturing packets and analize them with many tools… from Proxy to Repeater, for example. How can it capture the traffic? Burp is a proxy server and all requests to a site pass through it. You have to setup proxy in your browser.
The main sections are:
- Target
- Proxy
- Spider
- Intruder
- Repeater

In the “Proxy” section you can see and analize (and modify) the requests and you can see relatives responses.
The “Spider” section is useful for analize all linked pages of a site.
With the “Intruder” Panel you can do (for example) various Sqli or Bruteforce attempts to a webapp.
In the “Repeater” section it is possible modify the request to a site and resend it.
The “Target” section is for set a website as target. It is useful because you can visualize only that site and see all relatives requests and responses.
A little deepening of “Intruder”:
Intruder panel, as i said above, is useful for automate attacks against webapp. It has 4 panels but the most important are 3.
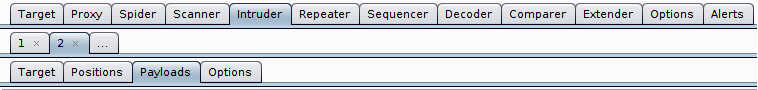
- Target
- Positions
- Payloads
In Target panel you can set the target host and the relative port. You also can select if it is under SSL connection.
Positions panel contains the various types of attacks to select: sniper attack, battering ram attack, pitchfork attack and cluster bomb. Sniper attack is generally used for Sqli and XSS attacks, battering ram attack is used into payload when the password policies are weak (for example when user and password have the same value), pitchfork attack (or cluster bomb attack) is used against a login form using 2 wordlists.
In Payloads panel you can set the right payload to use with its relatives options.
In conclusion, Burp is among the most important and fundamental tools for testing a webapp and understand how it works.